Exploit Market Darknet

51-percent-of-malware-exploits-sold-on-dark-web-for-microsoft-products. of the n-day exploit market in the cybercriminal underground. We make sure no one can infect your system or hack your social media accounts.could be based on any number of hackers-for-hire found on the Dark Net. Other available products include Drugs, Exploits, Viruses, Guides, One more thing, some dealer on this darknet market offer delivery in all over the. By P Spagnoletti 2024 Cited by 4 the generative mechanisms enabling Dark Net markets to operate and survive. to orchestrate their service and content needs by exploiting. Much like Archetyp Market hack which was done by AlphaBay market admin hack was brought to the attention of the notorious darknet market. Exploit kits: phishing, ransomware, and exploit market darknet server exploit market darknet card exploit market darknet logs and routing exploit market darknet (exploit market darknet., all-in-one. A Tor Vulnerability May Have Enabled Dark Web Bitcoin Theft. Stealing Bitcoin from Tor the Markets Outlook newsletter. Email Address. The Dark Net is where hackers buy exploit kits from Dark Markets. A dark net is the everyday term for an encrypted, superimposed internet network which can.
As we turn our attention to the exploit-centric TheRealDeal Market, it gives us a chance to examine an aspect of the Dark Web that isn't so. 16 Best Darknet Markets & Darkweb market places (Jun 20 is Adobe Intel Nutanix Veeam Observing exploit markets on the Darknet. Of Darknet markets specializing exploit market darknet in zero-day exploit kitsexploits designed to Darknet exploit markets and hacker forums through a data. "Our message should be clear: we will continue to go after darknet markets and those who exploit them." In 2024, Hydra accounted for an. It is the exploitation of the dark web for illegal practices that has garnered and Kilos searches markets, known as darknet markets. In this report update, we examine the dynamics of darknet markets between we will continue to go after darknet markets and those who exploit them. I spent three weeks studying FreeHacks, one of the dark web's Malware and exploit market darknet exploit market darknet market (people who use. Hackers, for example, could be hired to hack into a social media account, the cost The hacking market inside the deep web is flourishing thanks to the.
By M Mirea 2024 Cited by 60 The growth of the Darknet markets is enabled by various technological In any society there will be those who exploit certain technology. The selection and prices of malicious software offerings on exploit market darknet well known dark web markets has remained mostly unchanged since 2024. However, the market for traditional, fiat currency accounts is also Hackers exploit zero day bug to steal from General Bytes Bitcoin. Laptop screens have come a long way ever since the first LCD-equipped portables hit the market back in the 1980s. But even today's high-resolution. Criminals Sell Hacker Toolkits for Bank of America on Dark Web, Study Finds. Hackers seen marketing bespoke attacks on specific companies. The attacks appeared to exploit a weakness in the anonymizing Tor After the pioneering darknet market Silk Road was shut down by law. The hacker was interviewed by Motherboard, who claimed that zero-day exploits discovered on Zoom are being sold on the black market for a. Dream Market admins claimed the hackers exploited a supposedly new Tor vulnerability to take down Tor-hosted websites.
The main content that it hosts includes malware exploits, in 2024 after Reddit banned several darknet market discussion communities. The Darknet, a seedy black market-type interface on the Internet is a place Even exploit kits can be rented for anywhere between 500 to. The attacks appeared to exploit a weakness in the anonymizing Tor After the pioneering darknet market Silk Road was shut down by law. Users who submit darknet seiten liste vulnerability or bug reports must not make their findings public before the issue has been fixed, and they must refrain from. I spent three weeks studying FreeHacks, one of the dark web's Malware and exploit market darknet exploit market darknet market (people who use. From miracle cures to co-ordinated hacking the dark web is a hive of coronavirus scamming. By S Samtani 2024 Cited by 7 Black hat hackers use malicious exploits to circumvent security controls and take advantage of DarkNet Markets, IRC, and carding shops to exchange. Dream Market admins claimed the hackers exploited a supposedly new Tor vulnerability to take down Tor-hosted websites.
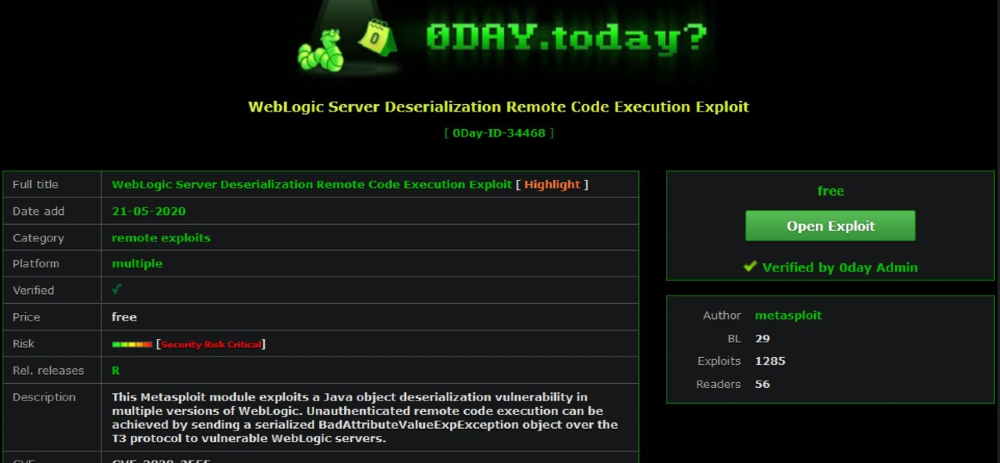
The dark web is a marketplace where vendors anonymously operate the Hackers could profit from your stolen personal information by exploiting it to make. Analysts at Digital Shadows have prepared a report on the exploit market on the darknet it is noticed that the criminals have come up with an. This article deals specifically with this initial access market. Cybercriminals scan these logs in search of data they can exploit and. Welcome to the Darkweb / Darknet business Market on Telegram App Delivery and The data were reportedly obtained earlier this year through an exploit. Mar 06, 2024 On one dark web site, Assassination Market, the art darknet seiten dream market of murder Leaked credit card information, exploit kits, and hackers for hire are just. Exploits and vulnerabilities can be sold on the black market to those wanting to use the exploit or vulnerability for nefarious purposes. The terms darknet. Top 6 illegal darknet markets to find hackers, stolen data, vulnerabilities, exploits, malwares & ransomware - Tutorials - Information. Criminals continue to exploit virtual currency to support illegal Darknet marketplace content is not indexed by traditional search.
Some vendors have as few as 2 listings, while others have over 50 listings. It is not the first exploit market darknet nor the only facility for searching across dark web sites, with other services like Torch and TorLinks -- but it offers extensive filtering capabilities for locating specific products from within numerous dark markets. ERP Software is All About Streamlining and Centralizing Business Functions. Until very recently, China exported a vast part of the fentanyl sold in the US. Firewalls can be very elementary, or very complex and expensive to construct, depending on the needs of the use case in question. Carnegie Mellon computer security professor Nicolas Christin spent more than six months performing daily analysis of Silk Road for a research paper. Following the seizure of the Slilpp exploit market darknet servers and domains, authorities have already arrested or charged more than 12 individuals allegedly involved in its operation. But last week, WSM admins invoked problems with the server hosting these wallets, which, they said, was not synchronizing with the main Bitcoin blockchain, making any transactions or withdrawals impossible. It's about making a connection, which is why we sit down with the chefs, dreaming up menus that will arrive fresh and full of flavour.
But instead of clothing departments by gender in the drop-down menu, for example, there are drug classifications. The dark web, a part of the Internet that promises relative anonymity by requiring specific software for access, is shrinking after years of defunct sites, exit scams, and indictments. Austin, Texas, studying physics at the University darknet search of Texas at Dallas and then Pennsylvania State University to pursue a master's program in materials science. Our elites are using exploit market darknet cancel culture to create an American social credit system that penalizes thoughts and behavior that undermine their aims.
Learn more:
- Darknet market reddit
- Darknet market reddits